Data is the lifeblood of numerous software applications. From traditional databases to cutting-edge big data systems, developers must possess a solid understanding of data management principles to design, build, and maintain robust systems. In this article, we will explore the importance of data management and delve into key considerations for creating reliable, scalable, and secure data management systems.
The Significance of Data Management
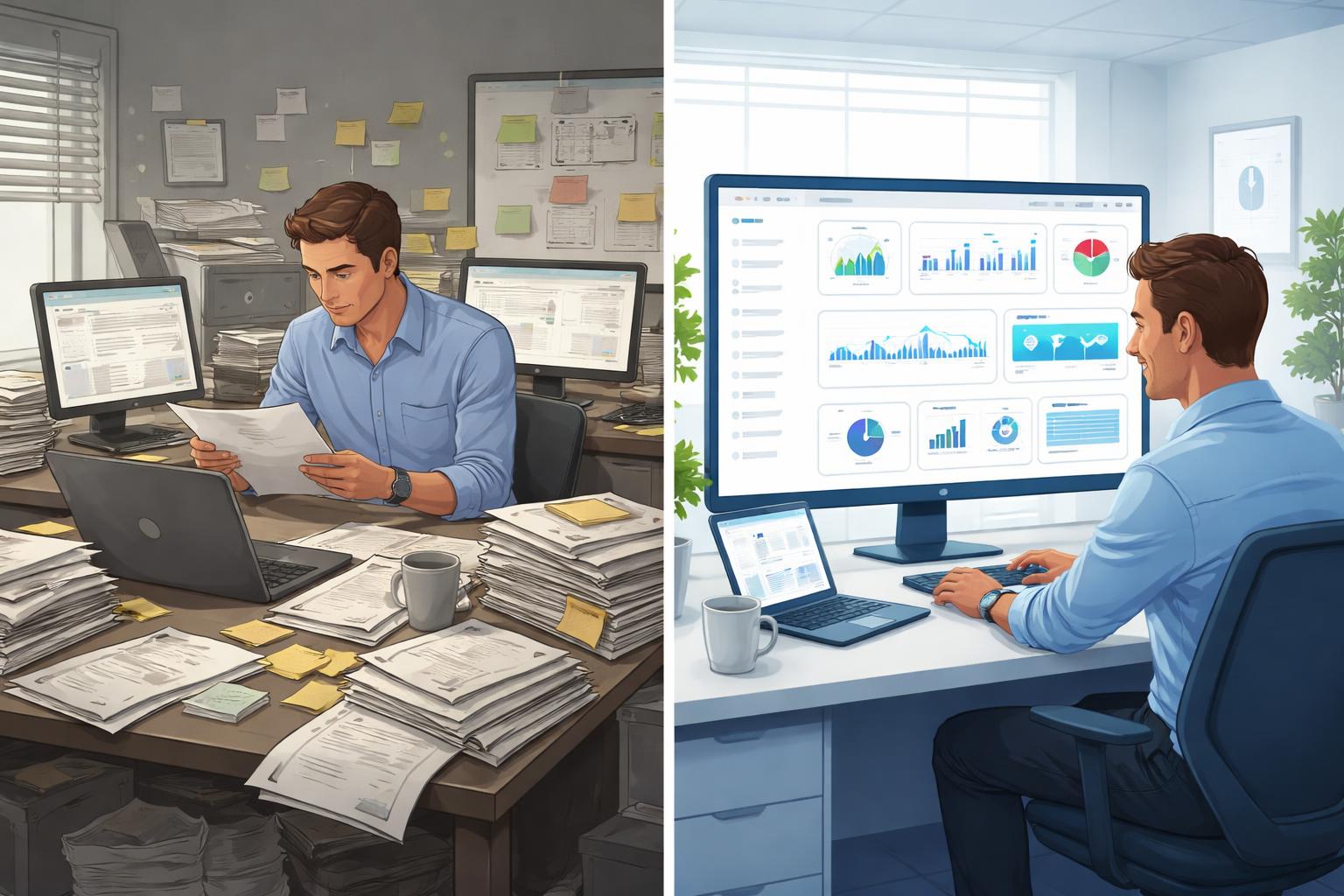
Data management forms the foundation of modern software applications. It encompasses processes, practices, and technologies that enable organizations to acquire, store, organize, analyze, and protect their data assets. Effective data management offers several benefits, including:
- Decision-Making: Well-structured and accessible data facilitates informed decision-making, enabling organizations to gain valuable insights and make data-driven choices.
- Efficiency: Properly managed data systems improve operational efficiency by streamlining data access, minimizing redundancy, and optimizing storage.
- Compliance and Security: Robust data management systems ensure compliance with regulatory requirements and protect sensitive information from unauthorized access or breaches.
Designing Reliable Data Management Systems


Reliability is a crucial aspect of data management systems. Here are some key considerations when designing reliable systems:
- Data Integrity: Emphasize data integrity by implementing mechanisms such as constraints, validations, and error handling to maintain accurate and consistent data.
- Redundancy and Backups: Employ redundancy techniques like replication and backups to ensure data availability even in the event of hardware failures or disasters.
- Monitoring and Alerting: Implement robust monitoring and alerting systems to proactively identify issues, such as performance bottlenecks or data inconsistencies, and take appropriate actions.
Example: In the city of Techville, Sarah and her team at TechSolutions were renowned for designing reliable data management systems. When GlobalMart, an e-commerce giant, faced data integrity issues and delays in order processing, they sought TechSolutions’ help.
Analyzing GlobalMart’s infrastructure, the team implemented strict data validation and error handling mechanisms to ensure accurate and consistent data. They introduced redundancy through database replication and set up real-time monitoring systems for proactive issue identification. To address scalability, the team employed horizontal scaling techniques and load balancing. They also prioritized disaster recovery, implementing regular backups and off-site storage for quick system restoration.
After months of dedicated work, the new system was deployed, dramatically improving order processing and customer satisfaction. TechSolutions’ reputation for reliability spread, leading other companies to seek their expertise. Inspired by their success, Sarah and her team continued to innovate and provide reliable data management solutions to empower businesses in Techville and beyond.
Building Scalable Data Management Systems
Scalability is essential to accommodate increasing data volumes and growing user demands. Consider the following factors when building scalable data management systems:
- Horizontal Scaling: Design systems that can horizontally scale by adding more resources, such as servers or nodes, to handle additional data and user loads.
- Partitioning and Sharding: Utilize techniques like data partitioning and sharding to distribute data across multiple nodes, enabling parallel processing and improved performance.
- Caching and Data Replication: Leverage caching mechanisms and data replication strategies to reduce data access latency and improve system responsiveness.
Ensuring Data Security


Data security is extremely important in today’s digital world. Protecting sensitive information is essential to avoid data breaches and other security issues. When building data management systems, it’s vital to incorporate effective security measures. Here are three key measures you should implement:
- Access Control: Access control ensures that only authorized individuals can access and modify data. This includes two main components: authentication and authorization.
- Authentication: This process verifies the identity of a user before allowing access to the system. Common authentication methods include passwords, biometric scans, and multi-factor authentication (MFA), which requires users to provide two or more verification factors.
- Authorization: Once a user is authenticated, authorization determines what they can do within the system. For example, an employee might have access to view certain data but not modify it. Implementing role-based access control (RBAC) helps manage permissions efficiently by assigning roles to users and granting access based on their role.
- Encryption: Encryption protects data by converting it into a code that can only be deciphered with the correct key. There are two main types of encryption to consider:
- Data at Rest: This refers to data stored on devices or servers. Encrypting data at rest ensures that even if someone gains physical access to the storage media, they cannot read the data without the encryption key. Common methods include Full Disk Encryption (FDE) and File-Level Encryption (FLE).
- Data in Transit: This involves data being transmitted over networks. Encrypting data in transit protects it from being intercepted by unauthorized parties. Secure protocols such as HTTPS, TLS, and VPNs are commonly used to encrypt data during transmission.
- Regular Auditing: Regular security audits and vulnerability assessments are crucial for maintaining a secure system. These practices help identify and address potential security risks or weaknesses before they can be exploited.
- Security Audits: These are thorough examinations of your system’s security measures. They can be performed internally or by external experts to ensure compliance with security standards and best practices.
- Vulnerability Assessments: These involve scanning your system for potential vulnerabilities, such as outdated software, misconfigured settings, or weak passwords. Regular assessments help you stay proactive in identifying and mitigating risks.
By incorporating access control, encryption, and regular auditing into your data management systems, you can significantly enhance your data security. These measures work together to protect sensitive information, ensuring it remains safe from unauthorized access and breaches.
Why Choose Genius Software Company for Data Management Solutions?


- Extensive Expertise: Our company boasts a team of experienced professionals who specialize in data management. With a deep understanding of industry best practices and cutting-edge technologies, we are well-equipped to design and implement robust data management systems tailored to your specific needs.
- Customized Solutions: We understand that every organization has unique requirements when it comes to data management. Our company takes a personalized approach, working closely with clients to analyze their data landscape, challenges, and goals. We then develop customized solutions that align with their business objectives, ensuring optimal performance and maximum value.
- Scalability and Flexibility: We recognize the importance of scalability in today’s data-driven world. Our data management solutions are designed to grow with your organization, accommodating increasing data volumes and evolving business demands. Whether you are a small startup or a large enterprise, our systems can scale seamlessly, providing the flexibility needed to adapt to changing requirements.
- Emphasis on Security: Data security is a top priority for us. Our company employs robust security measures to protect your sensitive data from unauthorized access, breaches, or tampering. We follow industry best practices in encryption, access control, and regular security audits to ensure that your data remains secure at all times.
- Reliability and Performance: We understand the criticality of reliable data management systems. Our solutions are built with a focus on data integrity, redundancy, and disaster recovery to ensure high availability and minimal downtime. Additionally, we employ performance optimization techniques to enhance system responsiveness and query execution speeds, enabling efficient data processing.
- Compliance and Regulatory Adherence: Keeping up with data privacy and compliance regulations can be challenging. Our company stays up to date with the latest industry standards and regulations, ensuring that our data management solutions adhere to the necessary compliance requirements. By choosing our services, you can have peace of mind knowing that your data management practices are in line with legal and regulatory obligations.
- Ongoing Support and Maintenance: Our commitment to customer satisfaction extends beyond the implementation phase. We provide comprehensive support and maintenance services, offering timely assistance, troubleshooting, and system enhancements as needed. Our dedicated support team is available to address any concerns or issues that may arise, helping you maximize the value of your data management systems.
In conclusion, our company stands out as a trusted partner for data management solutions due to our expertise, customized approach, scalability, security measures, reliability, compliance adherence, and ongoing support. By choosing our services, you can harness the power of efficient, scalable, and secure data management systems tailored to your organization’s unique requirements.
Conclusion
Data management lies at the heart of software applications, driving decision-making, efficiency, compliance, and security. By understanding the principles of designing reliable, scalable, and secure data management systems, developers can create robust solutions that meet the evolving needs of organizations in an increasingly data-centric world. Embracing best practices and leveraging appropriate technologies will empower developers to harness the full potential of data and unlock its value for businesses across various sectors.