At a time when data is the new oil, SaaS security has transcended being a technical checkbox into becoming an integral part of business strategy. With more and more mission-critical workflows being moved to the cloud, the stakes for SaaS service providers to deliver dependable SaaS data protection have never been greater. With increasing intensity of cyber attacks and regulatory bodies flexing their muscle, SaaS compliance is no longer simply a question of staying out of the penalty box—it’s about earning and maintaining trust with which to earn enterprise-quality clients.


For CTOs and CISOs, the job is two-pronged: they must defend a multi-tenant environment from ever-more sophisticated external attacks – such as denial of service attacks and ransomware – while also guaranteeing that internal data-management models comply with worldwide legal requirements. Enterprise security needs this to move away from reactive security patches and a practice of “security-by-design.” A high quality SaaS solution needs to reconcile rapid feature delivery with an extensible security base that can keep up with the changing landscape of healthcare, finance, and enterprise software needs.
To navigate this, you need to understand where the architectural decisions you make have positive or negative impact on your security posture. Whether you are building out a fintech platform, or storing patient data in a healthcare suite as we’ve done at Nymiti, your security framework is what makes your product ready to move from niche tool to enterprise solution. This article gives an overview of how the foundation for such trust can be effectively established – and preserved – by way of sophisticated protection models and sound governance.
Why Security and Compliance Define SaaS Trust
SaaS companies have transitioned from being simple service providers to becoming the primary custodians of global enterprise data. As businesses offload their internal processes to third-party platforms, the perimeter of the enterprise has effectively dissolved into the cloud. This shift has made SaaS platforms high-value targets for adversaries, making data security and compliance in SaaS applications the single most important factor in the procurement cycle. According to research by McKinsey, trust in digital ecosystems is now a primary driver of consumer and B2B choice, directly influencing market share and valuation.
Multi-tenancy architecture complexity further compounds the risk. Because in SaaS, unlike on-prem apps, we need to guarantee that “Tenant A” never has any data visible or accessible by “Tenant B”, even if they’re using the same infrastructure underneath. This isolation has to be total and verifiable. SaaS is also a global business, so even if this is only the law in one place it can be difficult for companies to comply with such laws in some places and not others, making compliance more of an engineering challenge than a simple legal one.
In the end, it’s security which is the quiet characteristic that defines a products ceiling. You can have the sexiest UI, or the fastest processing engine – but without proven dedication to data integrity and regulation compliance, enterprise doors will remain closed. In today’s market, security is not a cost; it is an offense and that helps you sell faster and at a higher price.
The Security Landscape in SaaS Applications
The threat landscape for SaaS is uniquely dynamic, driven by the accessibility of cloud interfaces and the interconnectedness of modern APIs.
Key Security Risks in SaaS
New SaaS platforms are hammered by advanced threats. API vulnerabilities are especially dangerous, given that they are the doors through which information moves from one service to another. Misconfigured APIs can result in mass data being leaked. Account takeover (ATO) attacks also top the list as does third-party integration risk, where a compromise in a lesser partner tool plays out on the main platform.
Multi-Tenancy Complexity
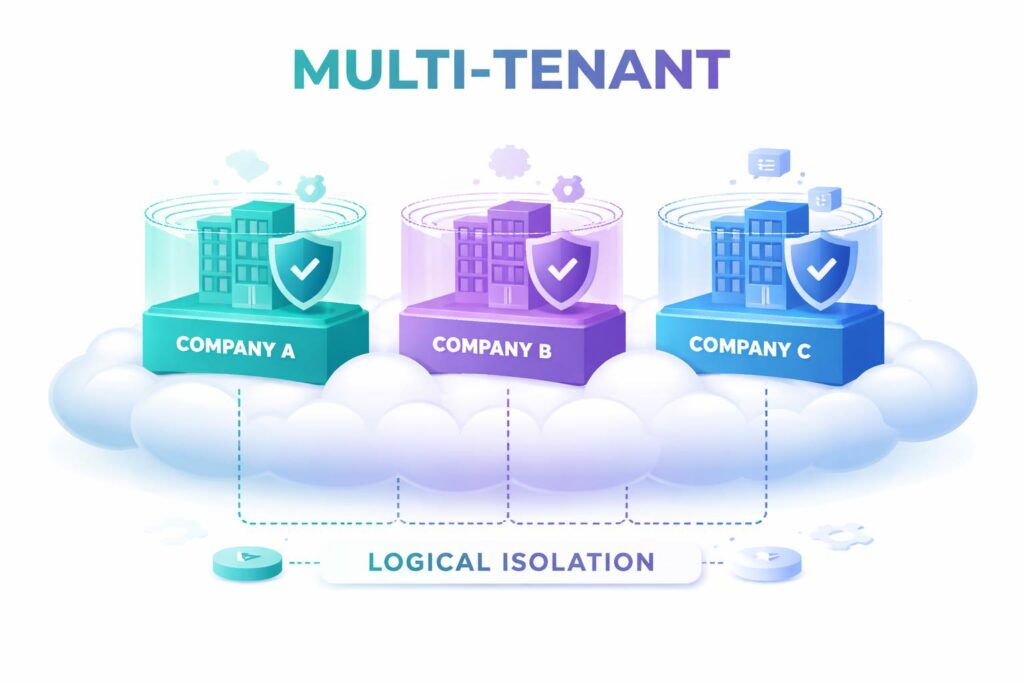
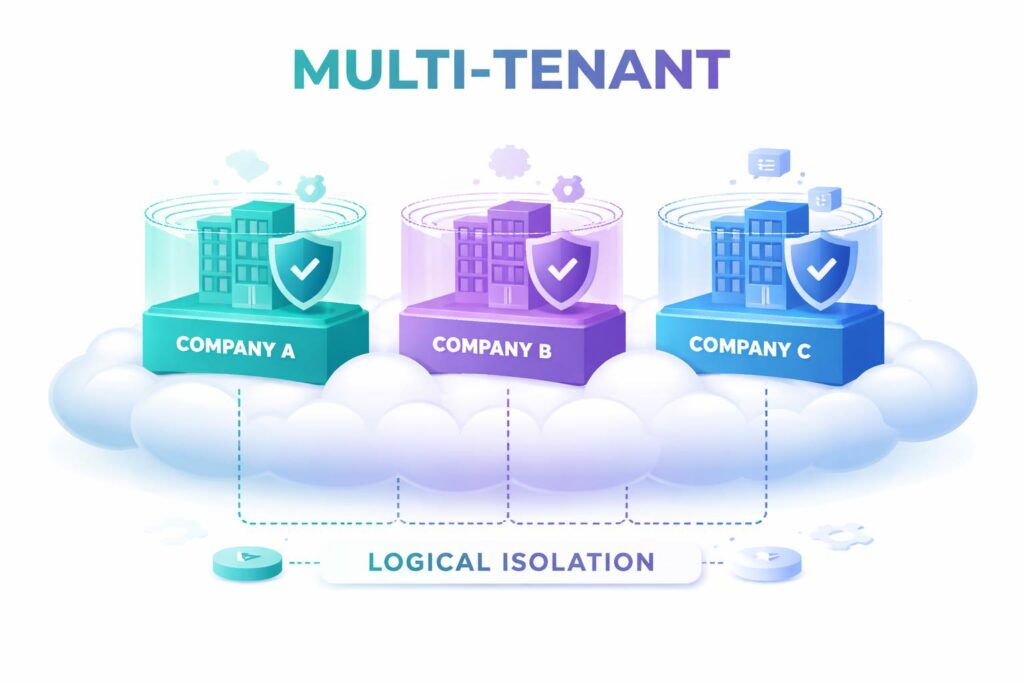
The “noisy neighbor” issue inside SaaS is not just a performance problem; it’s a risk of data leakage. Keeping logical separation in a multi-tenant database or container environment does not come for free. SaaS vendors need to secure tenant-specific encryption keys, leverage resource isolation effectively and ensure that the security is not compromised in other customers if one customer has a vulnerability related to its environment.
Demand for Enterprise-Grade Security
For enterprise clients , security claims are no longer taken at face value. They want “enterprise-grade” features like custom session times, audit logs, and integration with their own IdP. Satisfying these requirements is the key to moving upmarket (and landing contracts with six or seven-figure ARR) for a SaaS founder.
Core Principles of Data Security in SaaS
Building a secure SaaS product requires adhering to several non-negotiable architectural principles that prioritize protection at every layer.
| Principle | Technical Execution | Business Outcome |
| Zero-Trust | Verification of every request, regardless of origin. | Minimizes the blast radius of a potential breach. |
| End-to-End Encryption | AES-256 for data at rest; TLS 1.3 for data in transit. | Ensures data is useless to unauthorized interceptors. |
| Granular IAM | Role-Based Access Control (RBAC) and MFA. | Prevents unauthorized internal or external access. |
| API Security | Rate limiting, OAuth2, and continuous scanning. | Protects the primary data gateways from abuse. |
Zero-Trust Architecture
In a zero trust paradigm, the system operates on the premise that no user or device should be trusted by default, regardless of whether they are already inside or outside of the network perimeter. All access requests must be authenticated, authorised and kept current. It is crucial in SaaS systems where employees are working from home and integrations to other systems are being linked.
Encryption Across the Entire Data Lifecycle
Encryption is your last line of defense. SaaS-based apps have to use strong encryption for both at-rest data (data in databases or backups) and in-transit data (which moves between the user and the server). Advanced versions even offer “Bring Your Own Key” (BYOK) models so that the customer still owns their encryption keys, adding an extra level of trust.
Compliance Requirements for SaaS Platforms
Compliance is the formal validation of your security practices. While the requirements vary by industry, several frameworks have become global benchmarks.


- GDPR: Essential for any SaaS with European users, focusing on data sovereignty, the “right to be forgotten,” and strict breach notification timelines.
- SOC 2 (Type II): The gold standard for operational security in North America, auditing a company’s internal controls over a period of time.
- HIPAA: Mandatory for healthcare-related SaaS, requiring specific safeguards for Protected Health Information (PHI).
- PCI DSS: Required for platforms handling credit card information, focusing on secure transaction processing.
Architectural Foundations for Secure SaaS
A secure SaaS product is built on a resilient infrastructure that prioritizes isolation and observability.
Secure Cloud Infrastructure
The choice of tenancy—shared, hybrid, or isolated—dictates the security baseline. While shared tenancy is cost-effective, many enterprise SaaS providers move toward “Virtual Private Clouds” (VPCs) or isolated database instances for high-tier clients to provide a physical layer of separation.
Logging, Monitoring, and Threat Detection
Security observability is critical. You can not protect what you do not see. Having a centralized log system and SIEM (Security Information and Event Management) lets teams quickly notice what isn’t right. This is commonly combined with behavioural analytics to spot unusual conduct that could point to an insider threat or a hacked account.
Backup, Recovery, and Business Continuity
Data protection also means ensuring data availability. A robust Data engineering strategy includes automated, encrypted backups stored in geographically diverse locations. This ensures that even in the event of a ransomware attack or a major infrastructure failure, the service can be restored within the agreed-upon Recovery Time Objective (RTO).
How AI Strengthens SaaS Security and Compliance
AI is transforming SaaS security from a manual, reactive process into an automated, proactive shield.
Anomaly Detection and Early Threat Identification
Machine learning models can analyze billions of signals to establish a “baseline” of normal user behavior. When a user who typically logs in from London suddenly attempts to download a large volume of data from an IP address in a different region at 3 AM, the AI can automatically flag the event or lock the account before damage occurs.
Automated Incident Response
Speed is the most critical factor in breach mitigation. AI-driven “SOAR” (Security Orchestration, Automation, and Response) platforms can execute pre-defined playbooks in milliseconds—isolating compromised containers or revoking API keys—long before a human analyst could even open the alert.
AI-enhanced Compliance Monitoring
Compliance is often a point-in-time check, but AI allows for “continuous compliance.” By monitoring infrastructure changes against a set of regulatory policies, AI can alert Cloud security teams the moment a S3 bucket is made public or an encryption setting is downgraded. According to Statista, AI in cybersecurity is expected to grow significantly as companies seek to automate these governance tasks.
Challenges in Securing SaaS Applications
Despite the best tools, several human and structural hurdles remain.
- Speed vs. Security: Rapid release cycles in SaaS development can lead to security oversights if testing is not automated.
- Fragmented Data: Data spreading across multiple clouds and third-party tools makes unified governance difficult.
- Jurisdictional Complexity: Managing “Data Residency” requirements (e.g., keeping German data in Germany) is a major architectural burden.
- The Talent Gap: There is a global shortage of engineers who possess both deep SaaS knowledge and high-level security expertise.
Best Practices for Building Secure SaaS Applications
To build a platform that wins enterprise trust, follow these strategic recommendations.
Build Security Into the Architecture from Day One
Retrofitted security is expensive and often ineffective. Adopt a “Security-by-Design” approach where every new feature undergoes a threat model assessment and automated security testing (SAST/DAST) before it ever hits production.
Prioritize Data Governance
You must know what data you have, where it is, and who can access it. Implement a strict data classification policy (Public, Internal, Confidential, Restricted) and use automated tools to enforce these policies across your entire MLOps and production pipeline.
Work With Experienced Security Partners
For many scaling SaaS companies, it is more efficient to partner with experts rather than building a full security operations center (SOC) from scratch. Choosing the right Case studies to review when selecting a security partner is vital to ensure they understand the nuances of multi-tenant cloud environments.
Real-World Examples of SaaS Security Programs
Case Study 1: Healthcare SaaS (HIPAA Focus)
The Problem: A patient management platform needed to scale but was blocked by the inability to prove HIPAA compliance to large hospital networks.
Solution: They implemented an isolated tenancy model for PHI data with end-to-end encryption where only the client held the keys.
Result: Successfully passed audits for three major health systems and increased their enterprise pipeline by 200%.
Case Study 2: Fintech SaaS (PCI & SOC 2 Focus)
The Problem: A payment processing startup was seeing a rise in sophisticated API-based fraud attempts.
Solution: They deployed an AI-based anomaly detection layer within their API gateway to block suspicious traffic in real-time.
Result: Fraud-related losses dropped by 85%, and the company achieved SOC 2 Type II certification in record time.
Case Study 3: HR-Tech SaaS (GDPR Focus)
The Problem: An international recruitment platform struggled with the “right to be forgotten” across their massive, unstructured data sets.
Solution: They re-engineered their data layer using a “Global Data Controller” architecture that could identify and purge all PII associated with a single user across all backups and logs with one command.
Result: Eliminated the risk of GDPR non-compliance fines and streamlined their data privacy operations.
What is Next?
Now, data security and compliance are not just technical barriers to clear, but also among the strategic building blocks of success for existing SaaS companies. The greater the push across the industry for more sophisticated, AI-driven architectures, the differential to provide data protection and show regulatory compliance will only increase. Through investment in a zero-trust foundation, automated governance and culture of security-first development, SaaS companies build the “Trust Equity” they need to lead their sectors.
The promise of the future of SaaS is “Transparent Security” – where providers won’t just secure your data but they also offer you the means to verify at any time real-time that it’s secure. So as you grow and scale your platform, remember that a compromise costs more than money – it’s also your reputation. Construct for security now, and guarantee your future growth.
Is your SaaS platform ready for the next level of enterprise security and compliance? Our team of experts specializes in building secure, compliant architectures for high-growth SaaS products. Whether you need to prepare for SOC 2, HIPAA, or GDPR, we can help you build a scalable foundation that protects your data and your reputation. Contact us today for a comprehensive security and compliance audit.